SSL Certificates for Cryptography
HSYCO supports high-grade cryptography (TLS ECDHE RSA with AES 128 GCM SHA 256, 128 bit keys, TLS 1.2) to protect the communication between the web browser used by HSYCO web interface and the HSYCO web server.
This is considered secure for commercial applications (for example, on-line banking and e-commerce) and for the exchange of classified information.
HSYCO can use either self-generated certificates, or import certificates issued by a Certification Authority (CA).
A Java Virtual Machine version 8 or above is required to fully support HTTPS encryption, and to ensure compatibility with modern Web browsers.
Self-Generated Certificates
When the SSL certificate is generated by HSYCO, and it is therefore not signed by a Certification Authority recognized by the Web Browser, it is normal for the browser to display a security message during the first access to the site or periodically at the beginning of a new session.
This message asks the user a confirmation about the reliability of the server with which it is trying to start a secure session; since the certificate is not signed by a known CA, the browser can’t guarantee the identity of the server. By accepting the certificate, the connection is established and it is possible to proceed normally.
Anyway, even when the certificate is generated by HSYCO, all the exchanged data are protected by cryptography, as with signed certificates.
The auto-generated certificate guarantees the same level of cryptographic protection as an equivalent certificate signed by a CA.
The ServerName parameter in the hsyco.ini configuration file specifies the name used to generate the SSL certificate, necessary for the cryptography of the HTTPS Web traffic, and must correspond to the domain name through which HSYCO is accessible via the Internet.
The certificate is contained in the hsyco.keys file.
When HSYCO is started, if this file is not available, a new SSL certificate is automatically generated according to the name defined in ServerName.
Otherwise, HSYCO simply uses the certificate contained in this file, which could have also been generated by an official Certification Authority (CA).
If an official certificate has not been chosen, this file is thus created and managed by HSYCO without any manual intervention.
If the name defined in ServerName is modified, HSYCO will automatically recreate a new hsyco.keys file the next time it restarts.
Importing the Self-Generated Certificate on your Client
With some browsers and operating systems, like Safari on iOS, permanently importing the self-generated certificate in the local keystore could improve HSYCO's gui usability.
If the certificate is stored in the local keystore, the browser will always accept the HTTPS connection to HSYCO without asking for confirmation. On iOS, and in combination with the HTML5 persistent cache, saving the certificate locally will also significantly improve the gui initialization time.
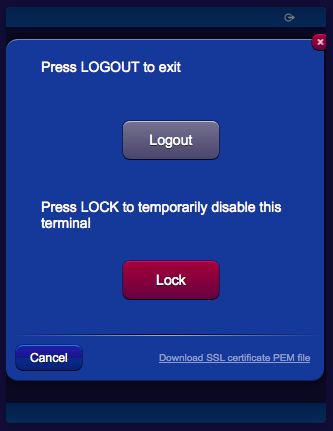
To download the server certificate's public key in PEM format, simply click the link in the logout panel, then follow the browser or operating system's instructions to save the certificate.
Certificates Issued by Certification Authorities
HSYCO can be configured to automatically request certificates to the ZeroSSL Certification Authority. A ZeroSSL account that supports their "REST API Access" is required.
In order to enable this feature, all relevant parameters must be configured in the Network tab of System Settings.
HSYCO will request a certificate when the current certificate is self-generated, or if it is expired or expiring in less than the number of days set with the HTTPSSLAdvanceRenewDays configuration parameter.
When a new certificate is issued by ZeroSSL, and downloaded by HSYCO, it will be saved in the hsyco.keys file and used by the HTTPS server for all new HTTPS connections. The downloaded certificate files, certificate.crt, ca_bundle.crt and private.key, are also saved to the hsyco.cert.save directory.
In order to issue a certificate, ZeroSSL must first verify the domain.
One way is to use HTTP verification. This is a fully automatic process, requiring no user interaction, but the unencrypted HSYCO HTTP server (not HTTPS) must be accessible from the public Internet on port 80 at the public IP address associated with the certificate's domain name.
Another option is to use email verification. ZeroSSL will send an email to the email address set with the HTTPSSLValidationEmail configuration parameter. To finalize the verification of your domain, simply grab the domain verification key, click the "Go To Verification Page" button to get to the verification page and submit the domain verification key.
HSYCO periodically checks with ZeroSSL if the certificate has been issued. Log messages are printed in the log and also at the bottom of the Network configuration page.
For example:
2022.03.16 18:19:22.443 - SSLCERTS: CSR created. Submitting to CA
2022.03.16 18:19:25.102 - SSLCERTS: Sending email verification request to CA
2022.03.16 18:19:27.247 - SSLCERTS: Email verification request successfully sent. Checking in 5 minutes
2022.03.16 18:24:28.719 - SSLCERTS: Sending certifcate status request to CA
2022.03.16 18:24:29.254 - SSLCERTS: Certificate has been issued by CA
2022.03.16 18:24:39.313 - SSLCERTS: Sending certifcate download request to CA
2022.03.16 18:24:39.930 - SSLCERTS: Certifcate successfully downloaded from CA
2022.03.16 18:24:39.930 - SSLCERTS: Importing certificate
2022.03.16 18:24:41.630 - SSLCERTS: Certificate successfully imported
2022.03.16 18:24:41.631 - Reloading HTTPS SSL Certificate
Note that, in a High Availability configuration, HSYCO slave will never request new certificates from the certification authority when it is not active